Start Date
Coming Soon
Program Fee
INR 58,410
Duration
40 + 24 Hours
Recognition
EC-Council
Establish
Yourself As
A World Class
Penetration
Testing
Professional
- Apply correct methodology in engagements
- Exploit IoT, SCADA, and Cloud systems
- Bypass the human factor (Social Engineering)
- Evade Enterprise Defenses
- Go Beyond Automated Tools
- Access complex segmented networks
- Write world-class reports!
Certified
Penetration Testing
Professional Program
What is the C|PENT Course?
A rigorous Penetration Testing program that, unlike contemporary Penetration Testing courses, teaches you how to perform an effective Penetration test across filtered networks. C|PENT is a multidisciplinary course with extensive hands-on training in a wide range of crucial skills, including advanced Windows attacks, Internet of Things (IoT) and Operational Technology (OT) systems, filtered network bypass techniques, exploit writing, single and double pivoting, advanced privilege escalation, and binary exploitation. In summary, there is no program of its kind in the world!

That’s why for the first time in the industry, the assessment for the Certified Penetration Testing Professional (C|PENT) is about multiple disciplines and not just one or two specialty types.
- The course is presented through an enterprise network environment that must be attacked, exploited, evaded, and defended.
- EC-Council’s C|PENT assesses a Penetration Tester’s skills across a broad spectrum of “network zones”.
- What makes the C|PENT different is the requirement to be provided a variety of different scopes of work so that the candidate can “think on their feet.”
- The result of this is that there are different zones representing different types of testing.
- Anyone attempting the test will have to perform their assessment against these different zones.
C|PENT is a 100% Hands-on Course featuring the industry’s most robust, in-depth, hands-on lab and practice range experience.
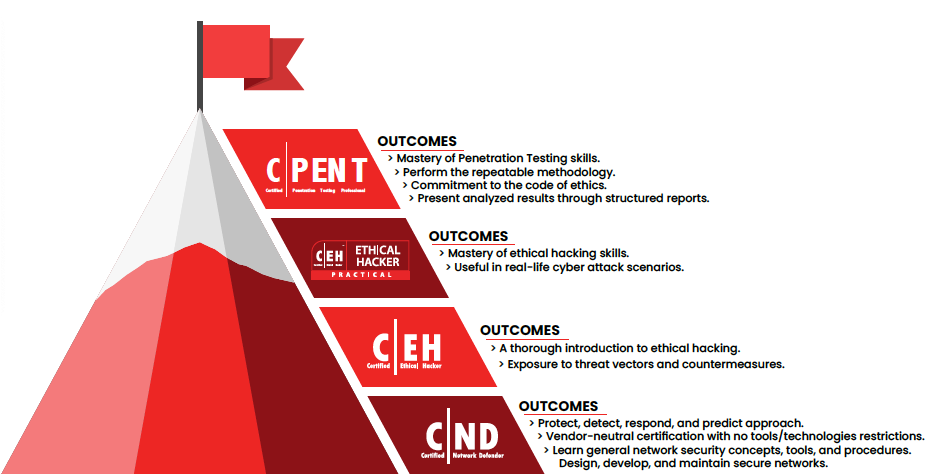
EC-COUNCIL’S VULNERABILITY ASSESSMENT AND
PENETRATION TESTING (VAPT) LEARNING TRACK
PROGRAM OUTLINE
Cover the fundamentals of penetration testing, including penetration testing approaches, strategies, methodologies, techniques, and various guidelines and recommendations for penetration testing.
Learn the different stages and elements of scoping and engagement in penetration testing.
Learn how to use techniques and tools to gather intelligence about the target from publicly available sources such as the World Wide Web (WWW), through website analysis, by using tools/frameworks/scripts, and so on.
Learn different social engineering techniques and perform social engineering penetration testing on a target organization.
Learn how to implement a comprehensive penetration testing methodology for assessing networks from outsiders’ perspectives. Learn the process attackers follow to exploit the assets using vulnerabilities from the outside of the network perimeter.
Learn how to implement a comprehensive penetration testing methodology for assessing networks from insider’s perspectives.
Learn how to implement a comprehensive penetration testing methodology for assessing the security of network perimeter devices, such as Firewalls, IDS, Routers, and Switches.
Learn how to analyze web applications for various vulnerabilities, including the Open Web Application Security Project (OWASP) Top 10, and determine the risk of exploitation.
Learn how to test various components of wireless networks, such as WLAN, RFID devices, and NFC technology devices.
Understand various threats to Internet of things (IoT) networks and learn how to audit security controls for various inherent IoT risks.
Understand OT and SCADA concepts and learn the process of testing various components of OT and SCADA networks.
Understand various security threats and concerns in cloud computing and learn how to perform cloud penetration testing to determine the probability of exploitation.
Understand the binary analysis methodology and reverse engineer applications to identify vulnerable applications that may lead to the exploitation of an information system.
Learn how to document and analyze the results of a penetration test and recommend post-penetration test actions
ADDITIONAL SELF-STUDY MODULES
- Penetration Testing Essential Concepts
- Fuzzing
- Mastering Metasploit Framework
- PowerShell Scripting
- Bash Environment and Scripting
- Python Environment and Scripting
- Perl Environment and Scripting
- Ruby Environment and Scripting
- Active Directory Pen Testing
- Database Penetration Testing
- Mobile Device Penetration Testing
- CEH Refresher
COMMON JOB ROLES FOR C|PENT
- Ethical Hackers
- Penetration Testers
- Network Server Administrators
- Firewall Administrators
- Security Testers
- System Administrators and Risk Assessment Professionals
- Cybersecurity Forensic Analyst
- Cyberthreat Analyst
- Cloud Security Analyst
- Information Security Analyst
- Application Security Analyst
- Cybersecurity Assurance Engineer
- Security Operations Center (SOC) Analyst
- Technical Operations Network Engineer
- Information Security Engineer
- Network Security Penetration Tester
- Network Security Engineer
- Information Security Architect
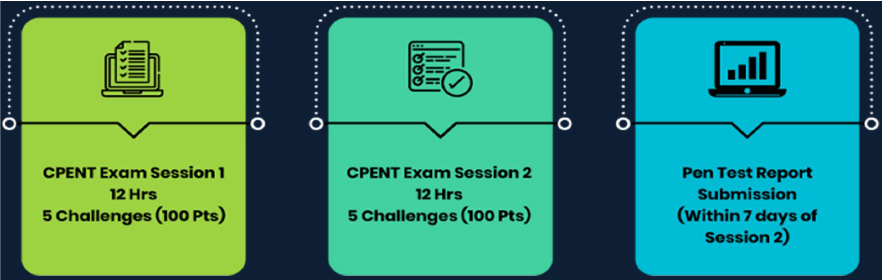
ATTAINING THE C|PENT CERTIFICATION
SINGLE EXAM, DUAL CERTIFICATION?
Should you score at least 70% in the C|PENT practical exam, you shall attain the C|PENT credential. However, if you are one of the few rare experts on the planet, you may be able to hit the minimum 90% to earn the Licensed Penetration Tester (LPT) Master Credential!
C|PENT is a fully online, remotely proctored practical exam that evaluates candidates through a challenging 24-hour performance-based, hands-on exam. The exam is broken into two practical exams of 12 hours each that will test your perseverance and focus by forcing you to outdo yourself with each new challenge. Candidates have the option to choose either two 12-hour exams or one 24-hour exam.